Crouching Chinese, Obscure Spy: Why is the Problem of Chinese Espionage Important for Ukraine?
31.07.2019
Internationally, the public opinion seems to have come to terms with the idea that “China is copying everything,” and this has become a common place both in smartphone reviews and in the analysis of the Chinese defence industry. But for some reason it is customary to perceive it in a reduced, or even comic way. They joke that while one Chinese worker is holding an “iPhone”, four others encircle it with a pencil – and other humoresques. Ha ha ha!
Funny or Scary?
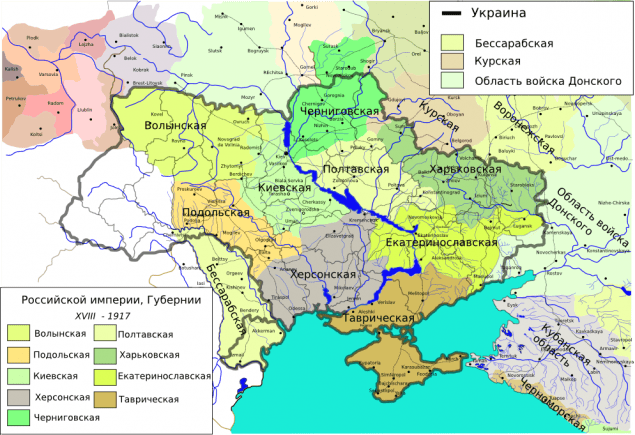
Behind the words “China is copying everything” one can imagine that painstaking work of hundreds of thousands of employees of China’s vast intelligence machine. Most of their dealings go unnoticed, however, some neat details sometimes leak into the news. For example, in Ukraine, a Chinese spy who had been working under the guise of an official scientific and technical officer was recently sentenced to 10 years — he was trying to take our secret scientific research in the field of the rocket and space industry to China. Agree, this is a little less ridiculous than jokes about “Chinese iPhone”.

In Poland, too, a spy scandal is now unfolding with far-reaching consequences. The Chinese spy worked undercover in the local regional structure of the giant Huawei, recruited agents, acquired secrets, and now the Polish authorities are thinking about sanctions against this company. We will get back to Huawei a little later, and now we will continue our international review.

In the US, Chinese cyber spies successfully plunder both commercial and military secrets. Russia faced China’s interest in their Bulava missiles and Roskosmos projects (the question remains, however, how much trust can we put in Russian justice)? The Czech Republic has covered the Chinese spy network. South Korea faced industrial espionage.
Few stories ever get into public access. However, any country, conducting its own technological research, sooner or later stumbles over increased attention from the Chinese intelligence services. It should just be taken for granted.
China in the Fog of War
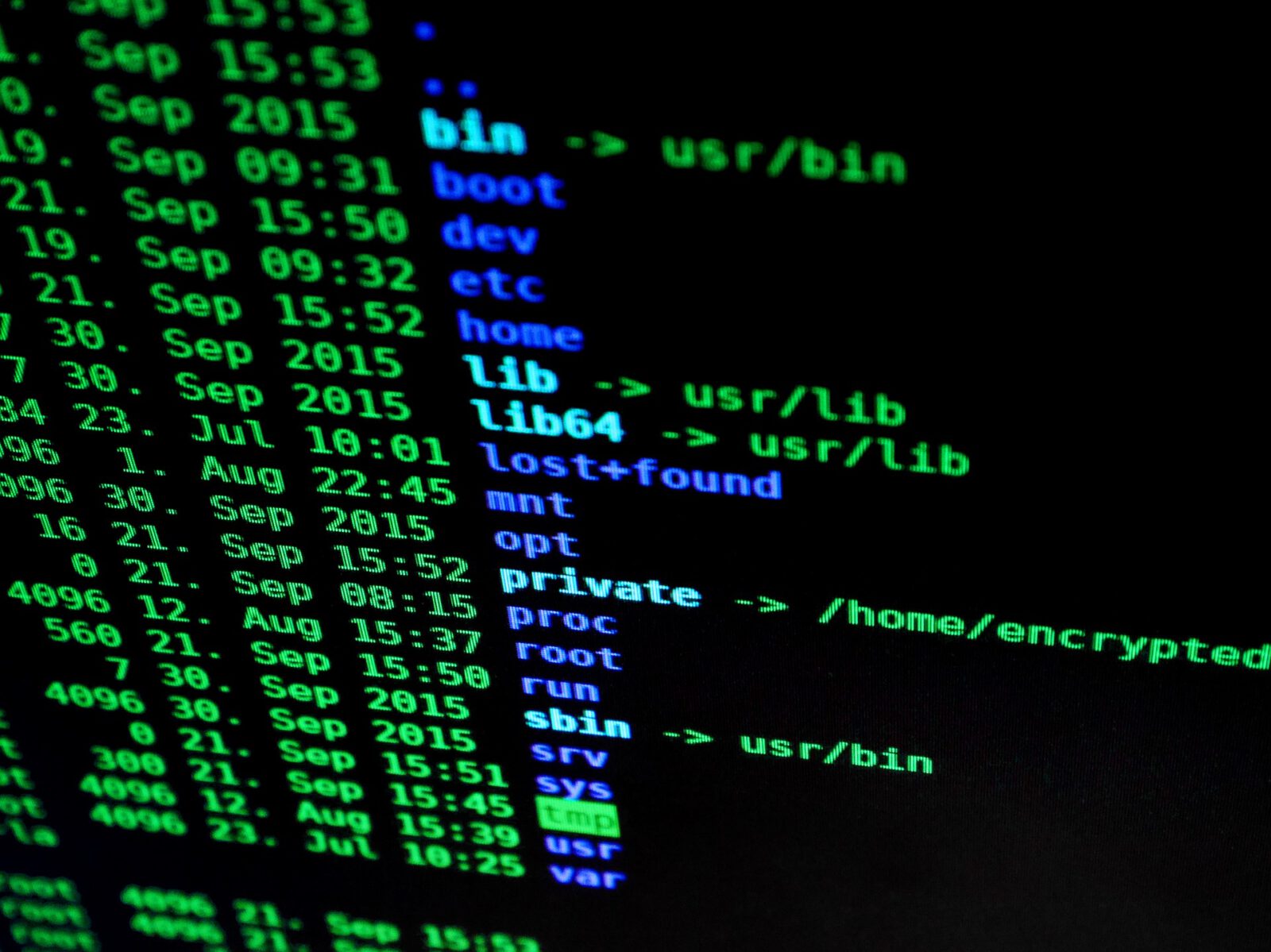
In addition to classic espionage stories, we see successful espionage automation projects. This is when, instead of the knights of the cloak and the dagger, the smartphones and other gadgets het to work, gathering information from millions of users with a frequent net.
Here again, it is appropriate to recall those merry jokes about “Chinese iPhones.” It happens that the treasured package from Aliexpress turns out to contain a surprise, and instead of normal operation, weird stuff starts happening accompanied by data theft. This is a fairly massive phenomenon that affects many Chinese brands.

But this is only the tip of the iceberg, because even stable Chinese devices may contain vulnerabilities aimed at collecting information. The products of manufacturers such as Huawei, ZTE, and others often jump into the focus of investigative journalism 1 , 2, 3). For the sake of justice, never before the investigation, journalists and experts could provide concrete evidence of espionage. This is understandable, since modern devices are complex, and it is difficult to track the “leakage” of information. Moreover, the affected companies are in no hurry to admit the loss of data, so as not to bring down their stock prices. And it’s very hard to separate real facts from manipulations in such a “gray” zone.

This situation is incredibly beneficial to China, which is almost invisible behind the smoke screen from scandals, assumptions, refutations, counterclaims and manipulations. Years go by, gigabytes of information flit back and forth. Trump declares war on Chinese companies, solemnly forgives them, journalists are poured another piece of “spy” information that they cannot verify. All this is very fun and greatly reduces the intellectual degree of discussion. So, following the link to the video below, two experts quietly blurt the problem, reducing everything to Trump’s greed. And somehow it falls out that gigabytes of data continue to circulate around the world, and no one can explain where they ultimately fall.
Ukraine is also concerned with this aspect of Chinese intelligence – we, like the whole world, are buying Chinese computer components, smartphones, network equipment. How much do we control this area of cybersecurity?
On the Invisible Frontline
Another gray area where Chinese spies play around is hacking. It is assumed that all Chinese hacker groups that steal both commercial and military secrets work for the Chinese government ( 1 , 2 ) “It is supposed” – after all, it is even more difficult to prove something in this unchartered territory than in the case of smartphone manufacturers, since cybercriminals do not have a binding to specific “hardware”, they work remotely. As for the analytical calculations, assumptions and conjectures – those can always be challenged. Therefore, the prospect of some legal suits against China with regard to regular attacks and hacks is missing. But regular cyber attacks do persist. China sweeps everything that is badly protected. Everything and everywhere, including, of course, Ukraine.
A Global Villain or Hostage to Circumstances?
It makes no particular sense to demonize China, whose relations with the world are largely determined by policies that other countries lead towards China. At first, the United States turned the People’s Republic of China into a global factory. Then the mood has changed, and China began to be portrayed as the America’s main strategic rival, without removing (?!) its functions of a global manufacturer. The schizophrenic war with their own factories is taken for granted by Western politicians, as one of the key elements of the game, and this forces China to play back. Being hung on the hook of technology, the Chinese are constantly looking for a way to get off this hook and develop their own tech. Sometimes, to reinvent the wheel once again, or to save on such reinvention, hence the series of spy scandals. Thus come spying attempts to infiltrate various spheres of business. For China, this is a logical and understandable strategy, which the country has been following for many years.
This should be treated calmly. Just do not forget that Chinese investments, as well as the Chinese economic partnership, can be accompanied by a small unpleasant appendage. And remember that Ukraine still has a number of valuable technological assets (and also continues to generate new ones), which China badly needs for development. Understanding our own interest, as well as interests of major global players should help us build a competent and foreign policy. Without illusions. Without too much chatter.